Have you ever been sitting, maybe waiting for an appointment at a company and watched people interacting with each other? Have you looked at door locks and wondered if you could open them? Have you ever sat in a lobby with open Ethernet ports and wondered what would happen if you plugged your computer into them? These are the kinds of questions that might make a good Red Team member.
What is a Red Team you ask? SANS defines as such: It is a process designed to detect network and system vulnerabilities and test security by taking an attacker-like approach to system/network/data access. According to the Military Red Team Handbook Red Teaming is: a flexible cognitive approach to thinking and planning that is specifically tailored to each organization and each situation. It is conducted by skilled practitioners normally working under charter from organizational leadership. It uses structured tools and techniques to help us ask better questions, challenge explicit and implicit assumptions, expose information we might otherwise have missed, and develop alternatives we might not have realized exist.
This most simple explanation that I discuss with people goes something like this. A Red Team, is a small to large group of individuals that are paid to think like criminals, act like criminals for the sole purpose of exposing critical issues to clients. Clients may not be aware of the found issues; at the end of the exercise a report is created to show how a system was compromised and what the client could do to prevent the issue in the future.
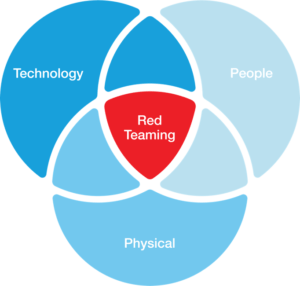
This Read Team process is different than just trying to hack into a system electronically. Red teaming involves lots of research and planning, it may and usually does include hacking systems electronically, but it also uses social engineering, physical break-in and physical surveillance.
One might ask, why do I need this type of high risk evaluation performed for my business, why isn’t it good enough to perform a vulnerability scan, an assessment or an Pen-test? The answer is simple, none of those types of assessments allow for obtaining passwords off of employees desks, cars, computers etc.
contact me if you are interested in this type of assessment!
